In an era where digital threats loom large, organisations must fortify their cybersecurity defences to protect sensitive data and ensure operational continuity. The Australian Cyber Security Centre (ACSC) has devised a comprehensive framework known as the Essential Eight (Essential 8) to guide organisations in enhancing their cybersecurity posture. In this article, we’ll delve into what the Essential 8 is, explore the key principles laid out by the ACSC, understand the Essential 8 Maturity Model, and shed light on the Australian Signals Directorate’s (ASD) Essential 8 strategies.
Understanding the Essential 8
The Essential 8 is a cybersecurity framework developed by the ACSC, a national authority in Australia dedicated to providing cybersecurity guidance and support. This framework serves as a strategic guide for organisations to mitigate the risk of cyber threats effectively. The Essential 8 comprises a set of prioritised strategies that, when implemented, significantly reduce an organisation’s exposure to a range of cyber threats, including malware, ransomware, and advanced persistent threats (APTs).
The ACSC Essential Eight
The ACSC Essential 8 is a set of eight strategies, grouped into two categories, designed to address the most prevalent cybersecurity threats. These strategies are practical, actionable, and represent a holistic approach to cybersecurity risk management. Let’s take a closer look at each of the Essential 8 strategies:
1. Application Whitelisting
Definition: Application whitelisting involves specifying a list of approved applications that are allowed to run on systems.
Purpose: By restricting the execution of unauthorised applications, organisations can prevent the installation and execution of malicious software.
2. Patch Applications
Definition: Regularly updating and patching applications to address vulnerabilities.
Purpose: Keeping software up-to-date is crucial in eliminating known vulnerabilities that cybercriminals may exploit.
3. Configure Microsoft Office Macro Settings
Definition: Adjusting settings to block macros from the web and only allow vetted macros.
Purpose: Macros in Microsoft Office documents are often exploited by attackers. Configuring settings helps mitigate this risk.
4. User Application Hardening
Definition: Configuring web browsers and email client settings to block malicious content.
Purpose: By hardening user applications, organisations can reduce the likelihood of users being exposed to malicious content.
5. Restrict Administrative Privileges
Definition: Limiting administrative privileges to essential personnel.
Purpose: Restricting access helps minimise the impact of a potential security incident and prevents unauthorised system changes.
6. Patch Operating Systems
Definition: Regularly updating and patching operating systems to address vulnerabilities.
Purpose: Just like patching applications, keeping operating systems updated is critical for security.
7. Multi-Factor Authentication (MFA)
Definition: Implementing multi-factor authentication for accessing systems and sensitive information.
Purpose: MFA adds an extra layer of security by requiring users to provide multiple forms of identification before gaining access.
8. Daily Backups
Definition: Regularly backing up important data and ensuring the backups are not accessible from the network.
Purpose: In the event of a cyber incident, having recent backups ensures the ability to recover data without paying ransomware fees.
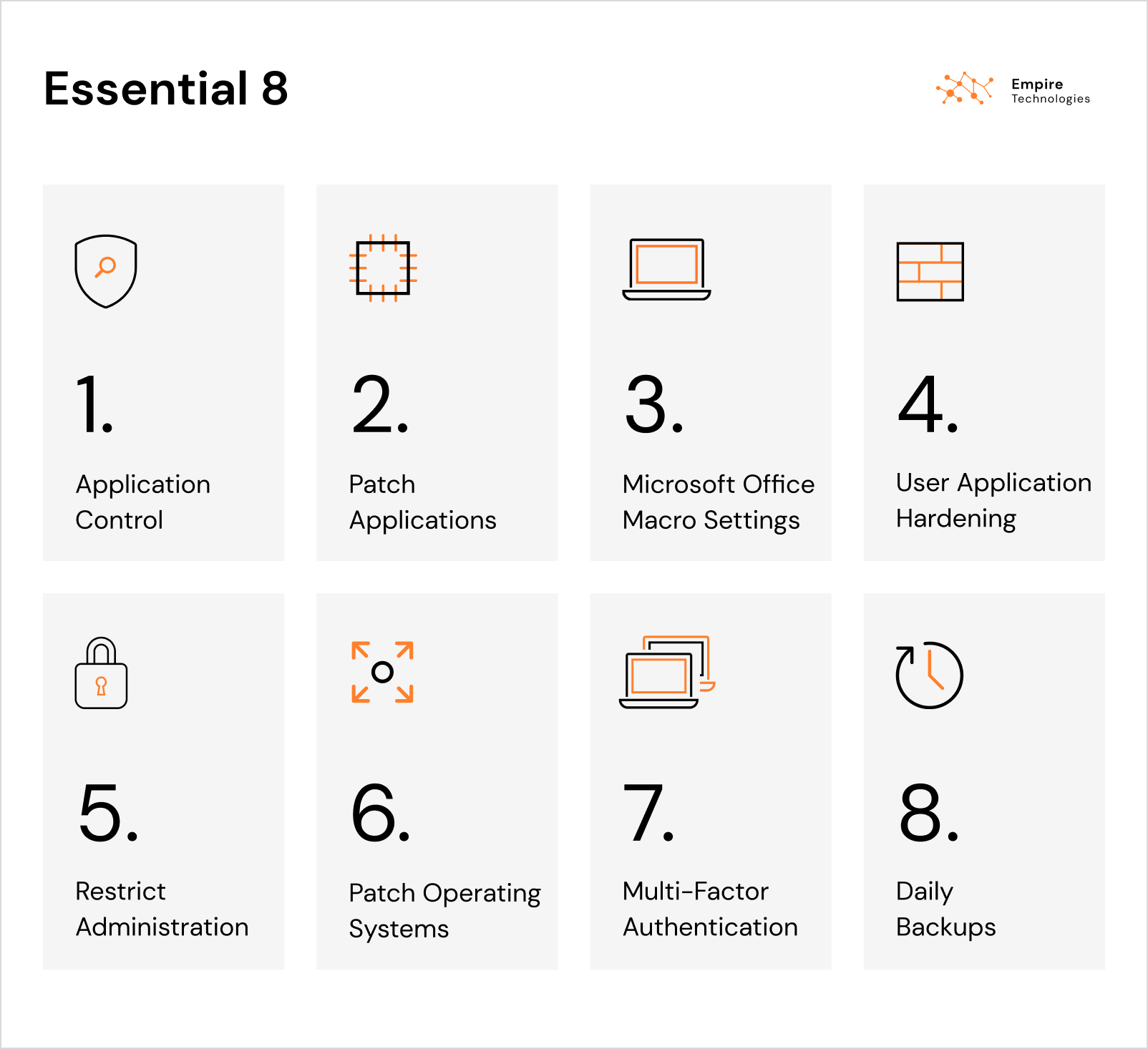
Empire Technologies – Essential 8 Diagram
Essential 8 Maturity Model
The Essential Eight Maturity Model is a tool that helps organisations assess their implementation of the Essential 8 strategies and determine their level of maturity in cybersecurity practices. The model consists of maturity levels ranging from “Ad Hoc” to “Optimised,” providing a roadmap for organisations to progress in their cybersecurity journey. For more information about the Essential 8 Maturity Model, read our page on Safeguarding your organisation using the Essential 8.
Ad Hoc
Organisations at this level have ad hoc or no processes in place to implement the Essential 8 strategies. There is limited awareness of cybersecurity risks.
Developing
Organisations are in the process of developing and implementing the Essential 8 strategies. Some elements may be in place, but the approach is not yet systematic.
Defined
Essential 8 strategies are defined, documented, and consistently implemented. Organisations at this level have a structured approach to cybersecurity.
Managed
At this level, organisations have established processes to monitor and manage the Essential 8 strategies. Regular reviews and updates are part of the cybersecurity routine.
Adopted
Essential 8 strategies are fully adopted, and organisations actively manage and update their cybersecurity measures based on evolving threats.
Integrated
Organisations have integrated the Essential 8 strategies into their broader risk management framework. Cybersecurity is a seamlessly embedded aspect of their operations.
Optimising
At the highest level of maturity, organisations continually optimise their cybersecurity measures. They proactively seek out and implement advanced cybersecurity practices.
ASD Essential 8 Strategies
The Australian Signals Directorate (ASD) has been at the forefront of cybersecurity in Australia, and its contribution to the Essential 8 is invaluable. The ASD Essential 8 strategies align closely with those laid out by the ACSC, emphasising the importance of a layered defence approach. See how you can implement the ASD Essential 8 Maturity Model on our Safeguarding your organisation using the Essential 8 page.
Let’s explore the ASD’s Essential 8 strategies:
Application Whitelisting
ASD’s Take: ASD encourages organisations to use application whitelisting to prevent the execution of malicious code.
Patch Applications
ASD’s Take: Regularly patching applications is highlighted as a fundamental strategy to minimise vulnerabilities.
Configure Microsoft Office Macro Settings
ASD’s Take: ASD underscores the significance of configuring macro settings to protect against macro-based malware.
User Application Hardening
ASD’s Take: The ASD emphasises the importance of hardening user applications to reduce the attack surface and protect against web-based attacks.
Restrict Administrative Privileges
ASD’s Take: Limiting administrative privileges is a key principle in preventing unauthorised access and mitigating security risks.
Patch Operating Systems
ASD’s Take: Regularly patching operating systems is crucial for addressing vulnerabilities and enhancing overall security.
Multi-Factor Authentication (MFA)
ASD’s Take: MFA is emphasised as a powerful tool to protect against unauthorised access and credential theft.
Daily Backups
ASD’s Take: Daily backups are recommended to ensure organisations can recover quickly and effectively in the event of data loss or ransomware attacks.

In the ever-evolving landscape of cybersecurity, the ACSC Essential 8 stands as a beacon, guiding organisations towards a more resilient and secure future. By implementing these strategies and progressing through the Essential 8 Maturity Model, businesses can fortify their defences and stay ahead of emerging cyber threats. The collaborative efforts of the ACSC and ASD underscore the importance of a unified approach to cybersecurity, where practical strategies and continuous improvement lead the way to a safer digital environment. As organisations embrace the Essential 8, they not only safeguard their own interests but contribute to a collective effort to create a more secure cyberspace for all.
Cyber Security